
As cloud infrastructure becomes increasingly complex and dynamic, Infrastructure as Code (IaC) has become a foundation of DevOps and cloud-native development. Terraform, a popular IaC tool developed by HashiCorp, allows teams to define cloud resources using simple, declarative code. However, with great power comes great responsibility and security often gets overlooked in the rush to deploy.
Snyk is a powerful security tool designed to identify misconfigurations and vulnerabilities in IaC files before they are deployed. Snyk is a developer-first security platform that integrates seamlessly into your development workflow, enabling teams to find and fix vulnerabilities in real time. Unlike traditional security tools that often slow down development, Snyk fits naturally into DevOps processes, providing clear, actionable insights without disrupting delivery speed. Its real-time scanning capabilities and automated fixes allow teams to address issues early in the software development lifecycle—making security a shared responsibility between Dev and security teams. When paired with Terraform, Snyk becomes a crucial part of a modern DevSecOps pipeline, allowing teams to ship infrastructure confidently, securely, and at scale.
Infrastructure-as-Code enables automation, repeatability, and version control for cloud resources. But it also creates a new attack surface. Misconfigured Terraform files can inadvertently:
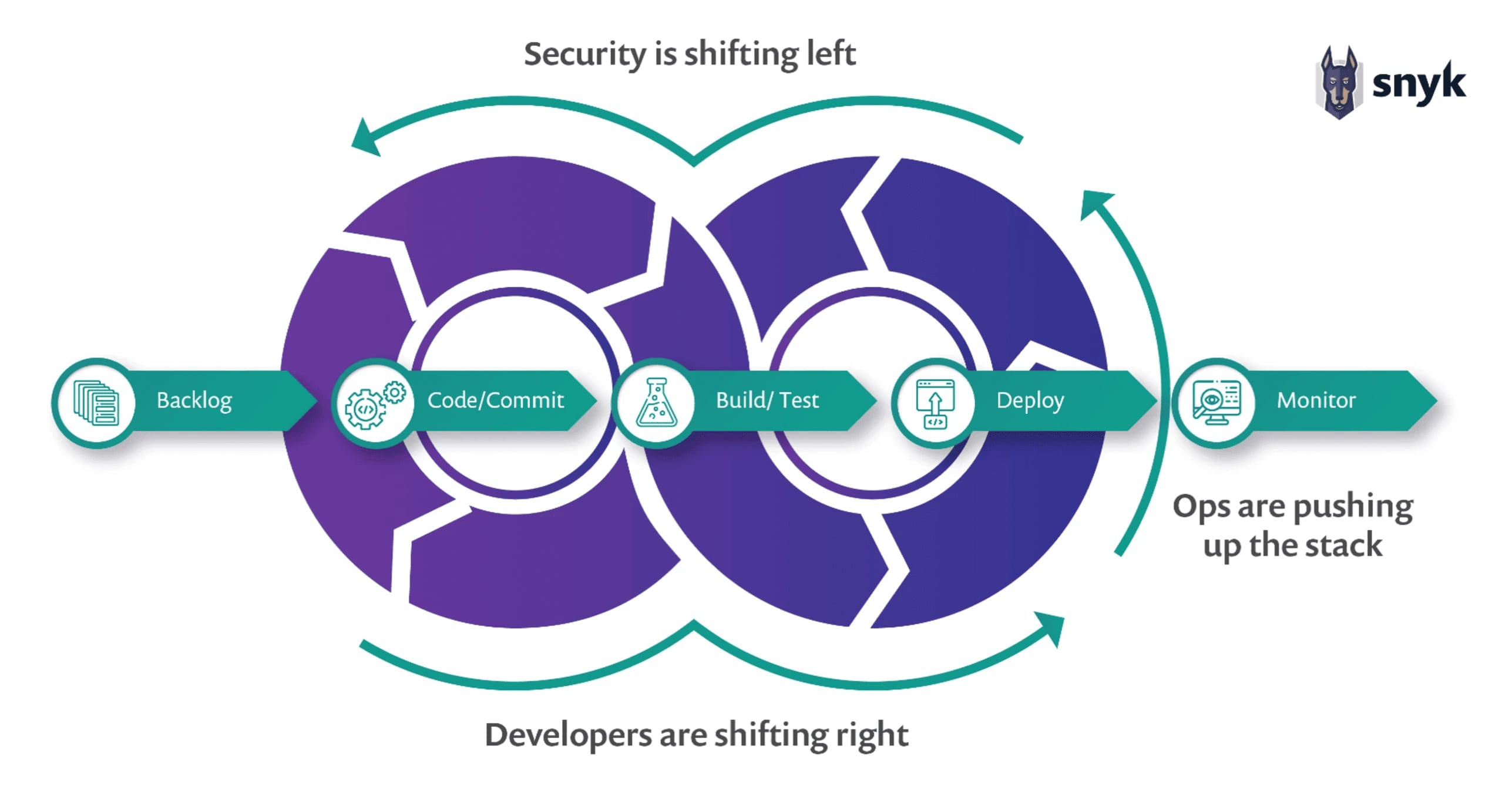
Since IaC defines how cloud infrastructure behaves, any misconfiguration in code gets reproduced every time the configuration is applied. This makes it vital to catch security issues early, preferably at the development stage — a key principle of shift-left security.
Snyk IaC is built to scan Terraform files (as well as other formats like Kubernetes YAML and CloudFormation) for misconfigurations that could lead to security or compliance risks.
Here’s how it fits into a secure DevOps workflow:
Snyk helps make security a developer-friendly concern, not a bottleneck that appears after infrastructure is deployed.
Key Features of Snyk IaC for Terraform
Scanning Terraform code with Snyk in GitHub Action
Integrating Snyk into GitHub Actions lets you automatically scan Terraform code for misconfigurations and security issues whenever changes are pushed. This approach adds an essential security layer early in your CI/CD pipeline.
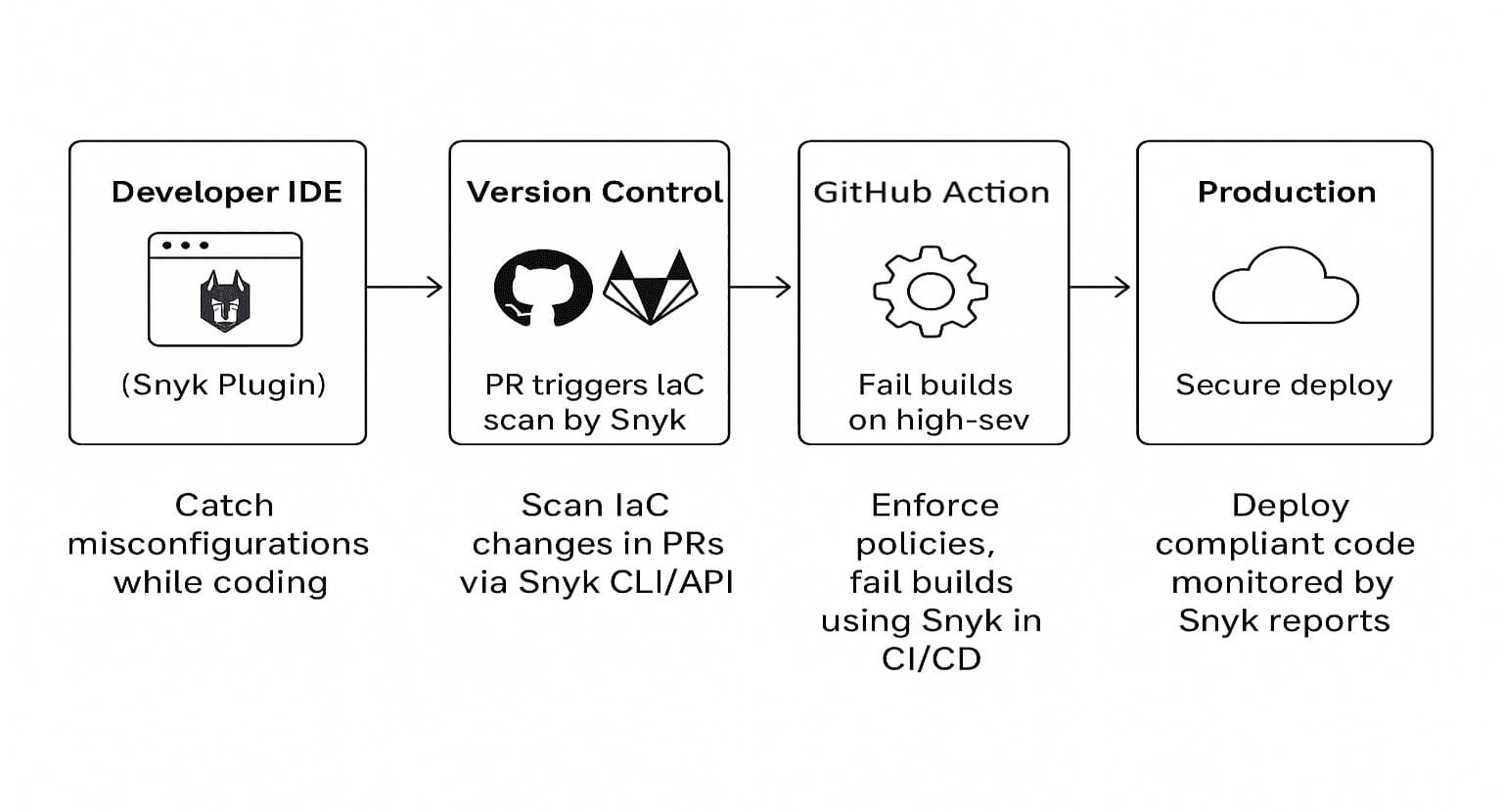
Below GitHub action workflow is configured to run the workflow each time new code is pushed in the repository. The workflow uses snyk test to scan your Terraform files for both security vulnerabilities and misconfigurations issues and then uploads a result to GitHub Security Code Scanning.


Altimetrik is committed to protecting your personal information. To apply for a position, you will need to provide your email address and create a login. Your information will be used in accordance with applicable data privacy laws, our Privacy Policy, and our Privacy Notice.
